FragAttacks, What You Need to Know.
FragAttacks, What You Need to Know.
Since its launch in 1997, there have been many attacks and security breaches, exploiting vulnerabilities in Wi-Fi networks. Hackers have targeted many industries and users to obtain personal data and information successfully. Thankfully, the Wi-Fi Alliance and researchers have continually tackled these issues by adding encrypted security features on Wi-Fi devices. This has been through introducing Wi-Fi Protected Access (WPA2 and WPA3), which prevents malicious attacks on the network, whether online or offline, and it’s been built into access points and user devices.
However, the Wi-Fi Alliance recently announced the discovery of a new security vulnerability, potential hackers can take advantage of to target any Wi-Fi device. It’s called FragAttack.
What are FragAttacks?
“Fragmentation and aggregation Attacks.”
FragAttack takes advantage of a series of design flaws and programming security vulnerabilities that affect Wi-Fi devices. It is based on how Wi-Fi devices receive, store, and process fragmented data that comes over the air. A total of twelve Common Vulnerabilities and Exposures (CVE) have been identified that trace back to 1997 when Wi-Fi was first introduced.
Studies have shown that hackers have to physically be within the radio range of a Wi-Fi network to exploit the internet traffic that sends information between Wi-Fi access points and user devices. However, this allows the attacker to steal private user information from anyone connected to that network.
Will they affect me or my customers?
Currently, there is no evidence of this issue affecting businesses or their customers using a Wi-Fi network.
However, as results indicate, all protected Wi-Fi networks, including old networks using Wired Equivalent Privacy (WEP), up to and including the latest Wi-Fi Protected Access 3 (WPA3) could still be potentially at risk.
What are the implications and impacts?
The vulnerabilities of FragAttack doesn’t affect the encryption of Wi-Fi or the cryptography meaning that hackers cannot break into an encrypted Wi-Fi network and obtain all the secured and private data of a network immediately onto the hackers’ devices. Therefore, FragAttack doesn’t pose this danger. FragAttack is based on how the data is fragmented when it is sent over the air. For instance, when sending a video across to another users’ device, the video doesn’t send as one component. It is broken down, and it’s fragmented, transmitted and then aggregated. The FragAttack is about the vulnerabilities of how this process happens and how the devices handle this process.
Hackers can craft a malicious plaintext frame and re-name packets on an existing Wi-Fi network, and send them to a different device on that Wi-Fi network. What happens then is that the device is tricked into believing that it is receiving specific information. However, the Wi-Fi devices fail to recognise that a hacker has manipulated the data it’s receiving. This then allows hackers to access the network and devices. Then hackers can intercept traffic to the device by tricking the end-user into using a corrupted DNS server. This then gives the hacker the potential to see the user’s screen, take screenshots, access user login and passwords, and even access apps.
These attacks are very complicated, and they usually work in stages, usually taking between two or three phases of action to accomplish a successful attack. The hacker must also, as mentioned previously, be very close to the Wi-Fi network, and there is the Man-in-the-Middle (MITM) attack. Establishing a successful Man-in-the-Middle (MITM) attack is hard to deploy. It requires the users to create and manipulate subframes/fragments precisely for the infrastructure to not block a MITM attack and getting the user on the device to use a malicious DNS server. There are a lot of steps that have to align to carry out a successful FragAttack. This makes it more challenging to implement, but it’s still possible.
What’s the Solution?
The solution is to patch all the devices, including client devices. Vendors will be releasing software patch updates soon to sort out these issues. Please keep updated on your vendor links here:
CommScope RUCKUS Products
https://support.ruckuswireless.com/fragattacks-ruckus-technical-support-response-center
Cambium Networks Products
Fixed wireless: https://www.cambiumnetworks.com/security/advisory-2021-03-fixed-wireless/
Access points: https://www.cambiumnetworks.com/security/advisory-2021-02-wi-fi-access-points/
WatchGuard Wi-Fi Products
https://techsearch.watchguard.com/KB?type=Security%20Issues&SFDCID=kA16S000000XeO7SAK&lang=en_US
In the meantime, to help mitigate the risk of vulnerabilities, please ensure that:
1. All the devices connected to the network are up to date with the latest software.
2. Change your passwords frequently on all devices, apps, and software.
3. Update devices with WatchGuard Security
What makes WatchGuard’s Wi-Fi security unique?
Wireless Intrusion Prevention System or WIPS is a term used in the Wi-Fi industry that refers to the prevention of Wi-Fi threats. WatchGuard’s WIPS is unlike any other competing Wi-Fi security solution on the market. Their patented technology ensures that you have the real, accurate and automated Wi-Fi protection your business needs.
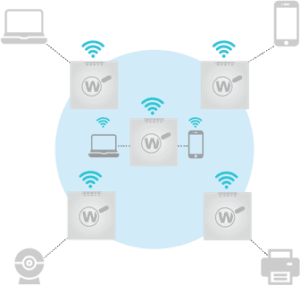
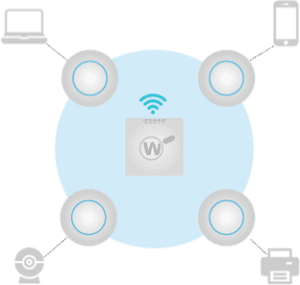
Each WatchGuard access point (AP) has the flexibility to operate as both an AP and a dedicated WIPS security sensor protecting any 3rd party brand AP. There are two deployment scenarios to choose from:
1. Wi-Fi and WIPS
Deploy WatchGuard APs managed with Wi-Fi Cloud and enjoy Trusted Wireless Environment compliant Wi-Fi, intelligent network visibility and troubleshooting features, captive portal, and location-based analytics.
2. WIPS Overlay
Just add WatchGuard APs as a security sensor to your existing infrastructure and protect any 3rd party brand APs 24/7. For example, you can see four Cambium/RUCKUS/Ubiquiti APs providing Wi-Fi access to different client devices and one WatchGuard AP configured as a dedicated WIPS sensor. The WatchGuard AP is not accepting connections from any Wi-Fi client but is there to simply monitor and protect the 3rd party APs 24/7 365-days a year.
No matter the scenario that you choose for your organisation, you need proof that the security solution that defends your business against Wi-Fi threats can provide automatic protection from the six known Wi-Fi threats.
Rogue Access Point – Allows hackers to bypass perimeter security
Rogue Client – Delivers malware payloads to the network after connecting to malicious APs
Neighbour Access Point or Client Mis association – Risks infection from connecting to other SSIDs while in range of the authorised AP
Ad-Hoc Network – Uses peer-to-peer connections to evade security controls and risk exposure to malware
“Evil Twin” Access Point – Lures users to connect to it to spy on traffic, steal data and infect systems
Misconfigured Access Point – Opens networks to attack as a result of configuration errors
If you would like further information on WatchGuard’s Wi-Fi Security and for exclusive pricing, please contact us at watchguard@purdi.com
For information on CommScope RUCKUS, contact us at: ruckus@purdi.com
For more information on Cambium Networks, contact us at: cambium@purdi.com
Alternatively, give us a call: +44 (0) 1488 647 647